ARTICLES AND TUTORIALS
We love writing about WordPress and how to get the most from our plugins. Read our insights into the WordPress world, our latest plugins tutorials, WooCommerce stats, and much more.
Premium quality plugins for WordPress & WooCommerce.
Expertly developed & supported by our oh-so-lovely team.
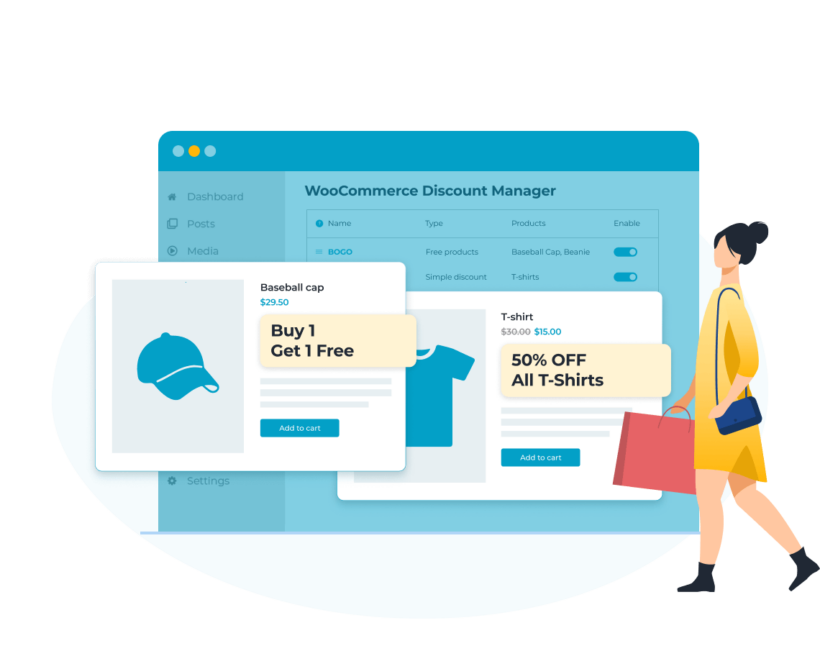
The most advanced WooCommerce discount plugin. Grow your sales with bulk discounts, storewide sales, BOGOF deals, role based pricing, and more 🚀
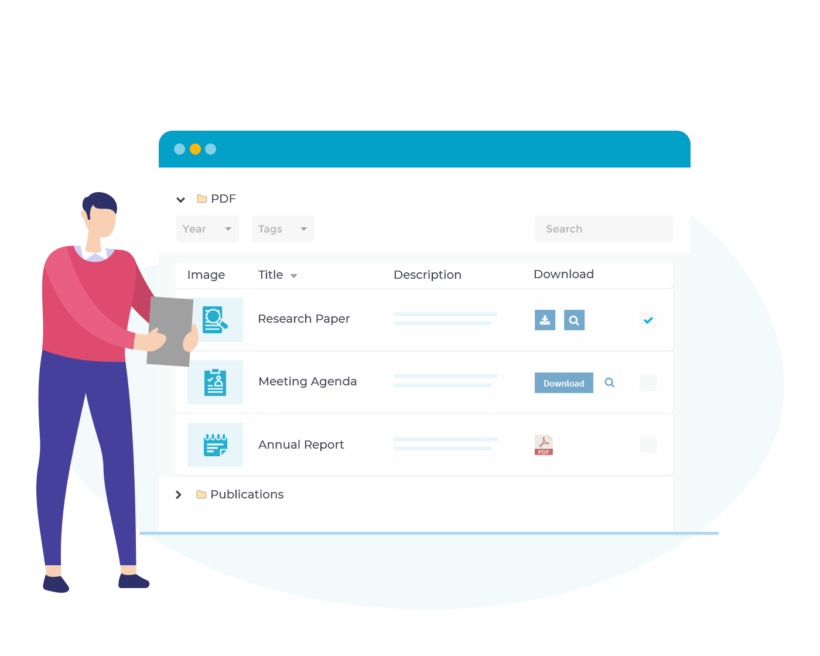
Discover the best way to create a document library in WordPress. Add and import documents, and display them in a searchable resource library. Supports any file type including PDF, audio and video.
Our bestselling plugin lists your WooCommerce products in a searchable table layout with filters. It's hugely popular for quick order forms, large product catalogs, restaurant order systems, wholesale layouts, and more.
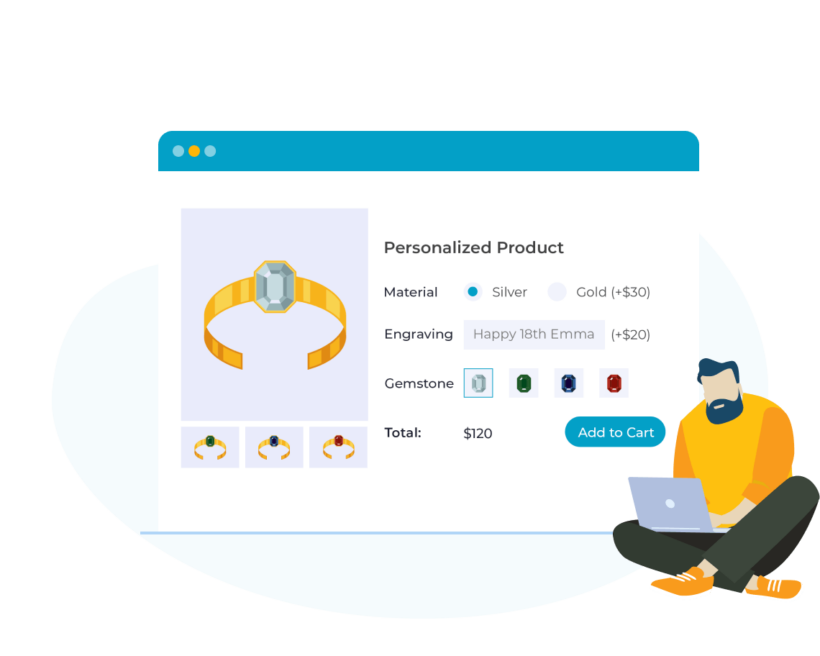
The most advanced product options plugin on the market. Allow customers to effortlessly personalize WooCommerce products and choose extra options and add-ons.

Are you still forcing customers to visit multiple pages to complete their purchase? Reduce abandoned carts by allowing customers to access their cart and complete the checkout directly in a fast cart popup.
We regularly publish tutorials about how to use our plugins for different use cases.
We provide detailed documentation with all our plugins, and unbridled support to help with any questions or problems you may encounter.
We love writing about WordPress and how to get the most from our plugins. Read our insights into the WordPress world, our latest plugins tutorials, WooCommerce stats, and much more.